Appleのコード署名APIの不具合により署名されていない悪意のあるコードが、サードパーティサービスで署名済のように見える不具合の詳細が公開されています。詳細は以下から。
![]()
2018年02月、サードパーティ製のセキュリティアプリやサービスで実際には署名されていないコード(Mach-Oバイナリ)がAppleの正規証明書で署名されたかのように見える不具合が確認されましたが、その不具合の詳細を米Okta, IncのセキュリティエンジニアJosh Pittsさんが公開しています。
I reported a rash of macOS code signing issues in security software which could make malicious code look like it was signed by Apple:https://t.co/fP7uBWk7Kh
— Josh Pitts (@midnite_runr) 2018年6月12日
Summary:
- A bypass found in third party developers’ interpretation of code signing API allowed for unsigned malicious code to appear to be signed by Apple.
- Known affected vendors and open source projects have been notified and patches are available.
- However, more third party security, forensics, and incident response tools that use the official code signing APIs are possibly affected.
- Developers are responsible for using the code signing API properly, POCs are released to help developers test their own code.
- The bypass affects Fat/Universal file format and the lack of verification of nested formats.
- Affects only macOS and older versions of OSX.
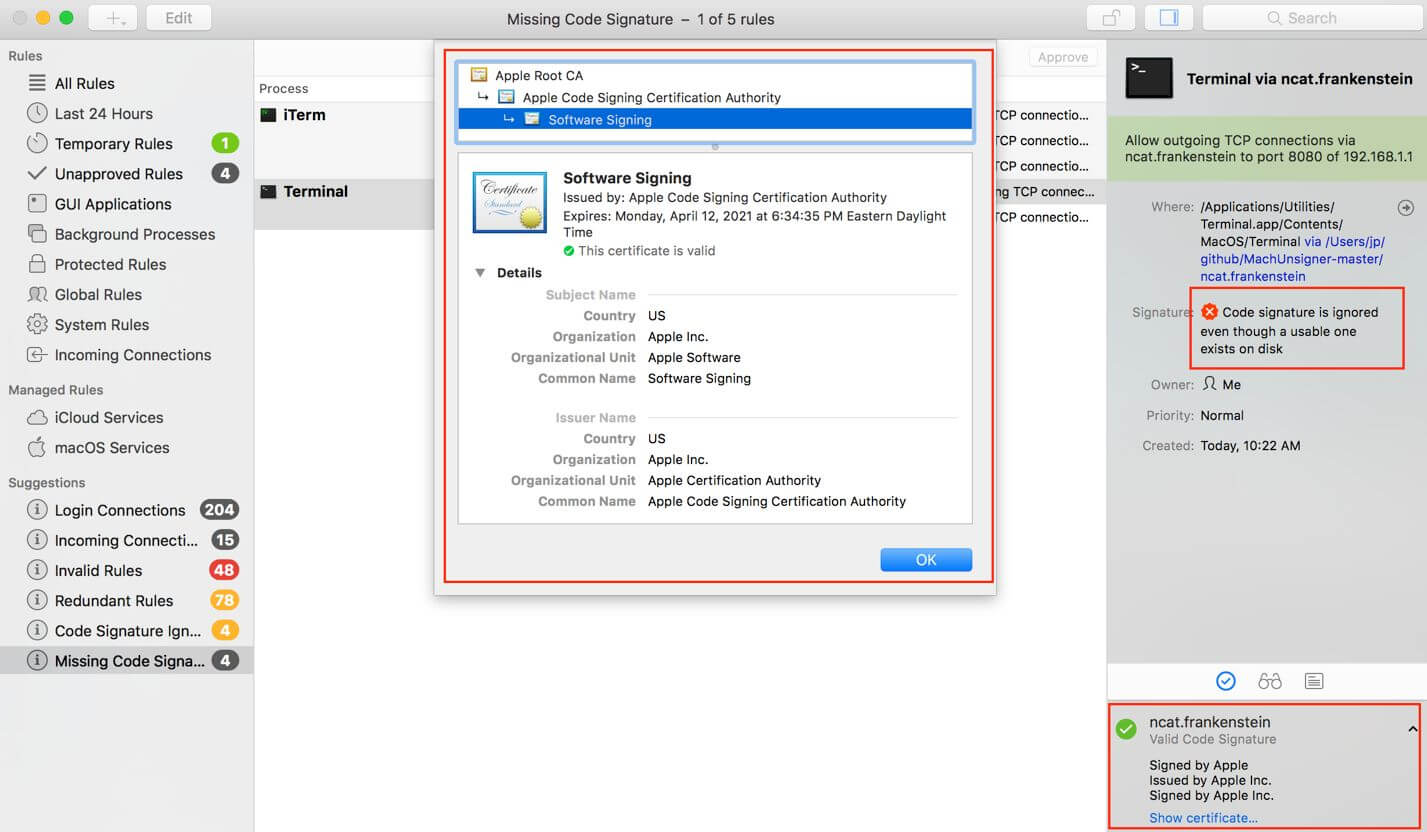
I can be Apple, and so can you – Okta
この不具合はAppleのコード署名APIがFat/Universalの署名をチェックするさいにネイティブCPUアーキテクチャ(現在はx86_64)の署名チェックを優先するためで、始めのMach-Oバイナリが正しく署名されていれば、悪意のあるi386コードをx86_64 macOSターゲットとしてコンパイルすることで、このコードが正しく署名されているとLittleSnitch(以下)などのサードパーティアプリなどに認識させることが出来るそうです。
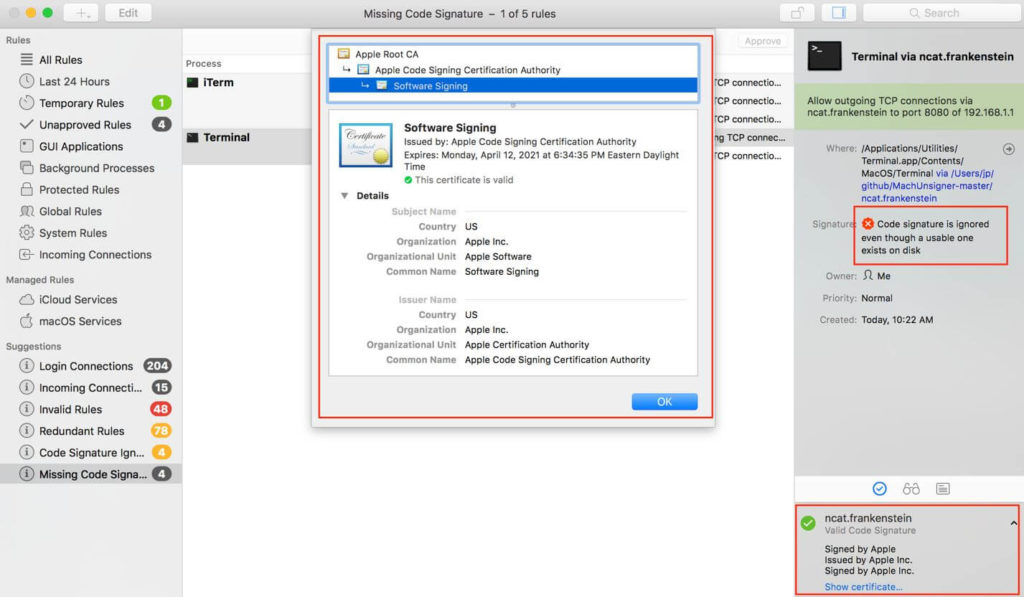
Conditions for the vulnerability to work:
- The first Mach-O in the Fat/Universal file must be signed by Apple, can be i386, x86_64, or even PPC.
- The malicious binary, or non-Apple supplied code, must be adhoc signed and i386 compiled for an x86_64 bit target macOS.
- The CPU_TYPE in the Fat header of the Apple binary must be set to an invalid type or a CPU Type that is not native to the host chipset.
[…]
March 29, 2018 – Apple stated that documentation could be updated and new features could be pushed out, but: “[…], third-party developers will need to do additional work to verify that all of the identities in a universal binary are the same if they want to present a meaningful result.”I can be Apple, and so can you – Okta
Joshさんはこの問題をAppleに報告しましたが、Appleはこの問題を修正するアップデートか新しい機能を追加する可能性を示したものの、現在のところはサードパーティ製のセキュリティサービスやアプリがユニバーサルバイナリの全てのIDをチェックするように求めたため、
影響を受けるアプリやサービス
- VirusTotal (CVE-2018-10408)
- Google Santa, molcodesignchecker (CVE-2018-10405)
- Facebook OSQuery (CVE-2018-6336)
- Objective Development LittleSnitch (CVE-2018-10470)
- F-Secure xFence, also LittleFocker (CVE-2018-10403)
- Objective-See WhatsYourSign, ProcInfo, KnockKnock, LuLu, TaskExplorer, others (CVE-2018-10404)
- Yelp OSXCollector (CVE-2018-10406)
- Carbon Black Cb Response (CVE-2018-10407)
Joshさんはこの問題が影響するサービスやアプリを検証し、各ベンダーに連絡、以上のサービスやアプリがこの問題を修正しているそうなので、GoogleのSantaやObjectiveのLittleSnitch、Objective-Seeの各セキュリティアプリを利用されている方は最新版へアップデートする必要があります。
About the issues with Code Signing Checks in Little Snitch: https://t.co/CMhc7z8oJm
— Little Snitch (@littlesnitch) 2018年6月13日

コメント