iOS 10.3.1で修正されたRCE脆弱性の詳細をGoogle Project Zeroが公開しています。詳細は以下から。
![]()
GoogleのセキュリティーチームProject ZeroのBeniaminiさんは現地時間2017年04月04日、Appleが「iOS 10.3.1」で修正したWi-Fiチップ上で任意のコードが実行される可能性のあるRCE脆弱性の詳細を公式ブログで公開しています。
Project Zero blog: "Over The Air: Exploiting Broadcom’s Wi-Fi Stack (Part 1)" by @laginimaineb – https://t.co/mXSgqLDA1v
— Ben Hawkes (@benhawkes) 2017年4月4日
We’ll focus on Broadcom’s Wi-Fi SoCs since they are the most common Wi-Fi chipset used on mobile devices. A partial list of devices which make use of this platform includes the Nexus 5, 6 and 6P, most Samsung flagship devices, and all iPhones since the iPhone 4. For the purpose of this blog post, we’ll demonstrate a Wi-Fi remote code execution exploit on a fully updated (at the time, now fixed) Nexus 6P, running Android 7.1.1 version NUF26K.
Over The Air: Exploiting Broadcom’s Wi-Fi Stack (Part 1) – Project Zero
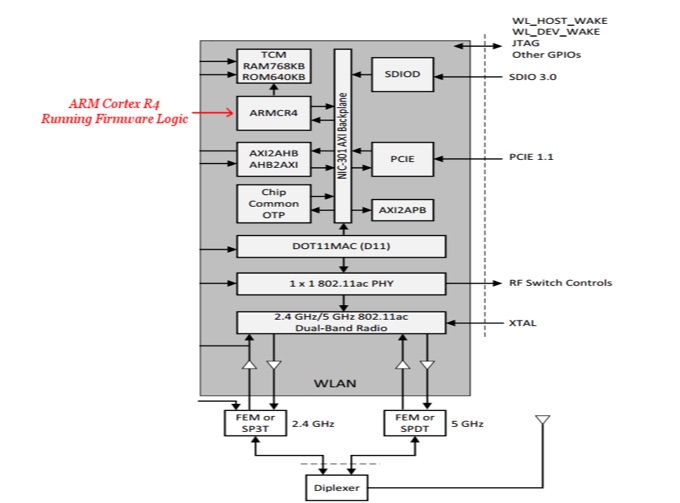
Beniaminiさんによると、この脆弱性はBroadcomのWi-Fiチップ(SoC)に搭載されているARM Cortex R4のMPU(Memory Protection Unit)の問題を利用し任意のコードを実行させるというもので、対象のBroadcomのWi-Fiチップを搭載したデバイスにはiPhone 4以降のiPhoneや、Samsungのフラグシップデバイス、Nexus 5や6, 6Pなどが含まれているそうです。
Ah-ha – while the MPU is initialised, it is effectively set to mark all of memory as RWX, making it useless. This saves us some hassle… We can conveniently execute our code directly from the heap.
So, at long last, we have an exploit ready!
Over The Air: Exploiting Broadcom’s Wi-Fi Stack (Part 1) – Project Zero
Googleは昨年12月にこの問題をBroadcomに報告し、Broadcomは新しいSoCでMPUやハードウェアセキュリティのメカニズムを強化しているそうですが、古いiPhoneなどはこのSoCを採用していないので、iPhoneやAndroidスマートフォンを利用されている方は最新のOSにアップデートすることをお勧めします。
Project Zero reported the issues to Broadcom in late December and the chipmaker was able to release fixes to vendors by late March, in some cases requesting an extension on Google’s usual 90-day deadline.
Beniamini says his analysis showed that the Wi-Fi SoC is “incredibly complex” but still “lacks basic exploit mitigations, such as stack cookies, safe unlinking”.It also didn’t use the Memory Protection Unit security feature available in the ARM Cortex R4 to protect access permissions over memory in RAM.
iPhone, Android hit by Broadcom Wi-Fi chip bugs: Now Apple, Google plug flaws – ZDNet
また、Beniaminiさんはこの問題を解説したブログPart.2を公開する予定で、そこではデモも行いたいとコメントしているので、興味のある方はチェックしてみてください。



コメント
broadcomは製品のデータシートを一般に公開しないし、不具合発生時の解析サービスに
ウザい条件を付けているので、問題が起きると無視されがち。