Macに保存されたiPhoneのバックアップやパスワードなどを盗み出すマルウェア「XAgentOSX」が発見されたそうです。詳細は以下から。
![]()
昨年(2015年)、ロシアのハッキンググループAPT28によりiOS端末上の情報を集め盗み出すマルウェア「XAgent」が発見され話題になりましたが、Bitdefender LabsによるとXAgentと同様の特徴を持ち、Mac上に保存されたパスワードやスクリーンショットを集め盗み出すMac版「XAgentOSX」が新たに確認されたそうです。
New Xagent Mac Malware Linked with the APT28 https://t.co/LKkgF4QtVf
— BitDefenderLabs (@BitDefenderLabs) 2017年2月14日
APT28 operators have upped their game – the Xagent payload now can target victims running Mac OS X to steal passwords, grab screens and steal iPhone backups stored on the Mac. Last year what appears to be one of the largest cyber-espionage campaigns ever, allegedly linked to the Russian territory.
The sample we are discussing today has been linked to the Mac OSX version of Xagent component from Sofacy/APT28/Sednit APT. This modular backdoor with advanced cyber-espionage capabilities is most likely planted on the system via the Komplex downloader.
New Xagent Mac Malware Linked with the APT28 – Bitdefender Labs
ターゲットとなるデータ
このマルウェアは感染するとバックドアを作成し、Appleのドメインに偽装された遠隔のコマンド&コントロール(C&C)サーバーと通信が確立すると、幾つかのモジュールを実行しMac上に保存された情報を集め、
C&Cサーバーリスト
- 23.227.196[.]215
- apple-iclods[.]org
- apple-checker[.]org
- apple-uptoday[.]org
- apple-search[.]info
上記のC&Cサーバーが指令があればアプリケーションのリスト、iPhoneやiPad(以下のディレクトリ)のバックアップデータ、スクリーンショット、Firefoxに保存されたパスワードなどのデータを転送するそうです。
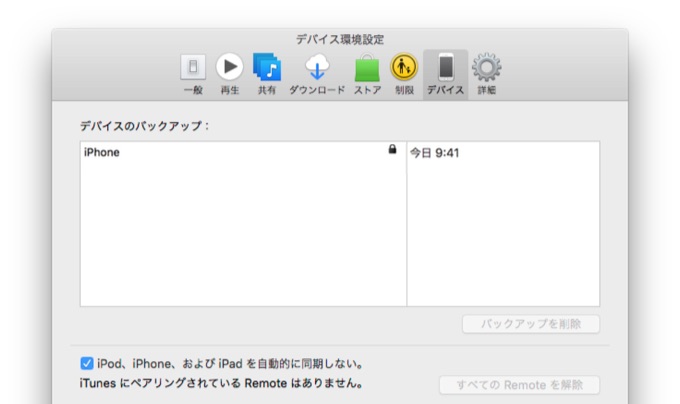
~/Library/Application\ Support/MobileSync/Backup/
Where do the Mac OS spy modules fall into place?
The analysis reveals the presence of modules that can probe the system for hardware and software configurations, grab a list of running processes and run additional files, as well as get desktop screenshots and harvest browser passwords.
But the most important module, from an intelligence-gathering perspective, is the one that allows the operator(s) to exfiltrate iPhone backups stored on a compromised Mac.New Xagent Mac Malware Linked with the APT28 – Bitdefender Labs
対策
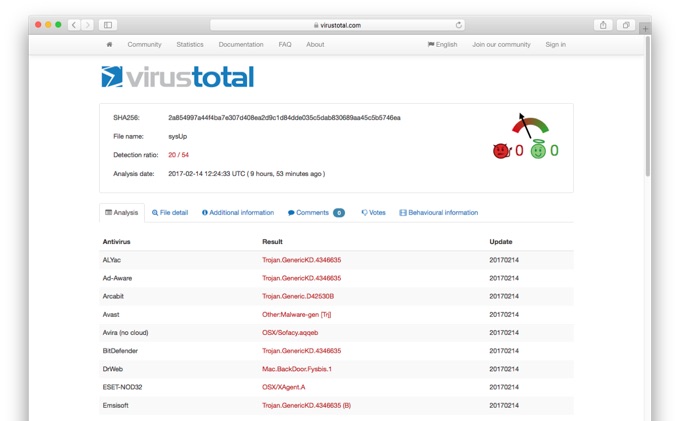
Bitdefender Labsは今後このマルウェアのさらに詳しい情報を開示する予定だとコメントしていますが、既に同社のウィルス対策ソフト「Bitdefender」シリーズを含め幾つかのウィルス検索エンジンがこのマルウェアの検出に対応しているので、心配な方はVirusTotalを参照し、Macのスキャンを実行してみてください。
- New Xagent Mac Malware Linked with the APT28 – Bitdefender Labs
- New Mac malware pinned on same Russian group blamed for election hacks – Ars Technica
- XAgentOSX: Sofacy’s XAgent macOS Tool – Palo Alto Networks Blog



コメント