OpenCLとNVIDIA GPUを使用して動くRootkit&Keylogger「Jellyfish」のMac版「MAC_JELLY」が公開予定だそうです。詳細は以下から。

Jellyfishとは?
先週匿名の開発者(チーム)x0r1がGPUベースのRootkit&KeyloggerのProof-of-Concept (PoC)「Jellyfish」をGitHubに公開し、Arc Technicaなどで話題になっていましたが、このJellyfishがLinuxからWindowsそしてMacに移植され始めているようです。
GPU-based rootkit and keylogger offer superior stealth and computing power http://t.co/pDKN9LUfiy by @dangoodin001
JellyfishはOpenCL APIとNVIDIA GPUを使用し動作し、DMAを介してCPUメモリを監視しキーボードバッファを手に入れ、GPUを使用することにより(クレジットカードナンバーなどを)高速に解析することが可能だそうで、現在GPUベースのマルウェアを解析するツールが無いためこのマルウェアを特定するのが困難だと説明されています。
Jellyfish is a Linux based userland gpu rootkit proof of concept project utilizing the LD_PRELOAD technique from Jynx (CPU), as well as the OpenCL API developed by Khronos group (GPU). Code currently supports AMD and NVIDIA graphics cards. However, the AMDAPPSDK does support Intel as well.
Some advantages of gpu stored memory:
・No gpu malware analysis tools available on web
・Can snoop on cpu host memory via DMA
・Gpu can be used for fast/swift mathematical calculations like xor’ing or parsing
・Stub/signature generation
・Malicious memory may be retained across warm reboots. (Did more conductive research on the theory of malicious memory still being in gpu after shutdown)Requirements for use:
・Have OpenCL drivers/icds installed
(Fun fact: Mac OS X boxes come pre-installed with OpenCL)
・Nvidia or AMD graphics card (intel supports amd’s sdk)
[x0r1/jellyfish – GitHub]
Jellyfishのベース
Jellyfishは2013年に公開された論文”You Can Type, but You Can’t Hide: A Stealthy GPU-based Keylogger
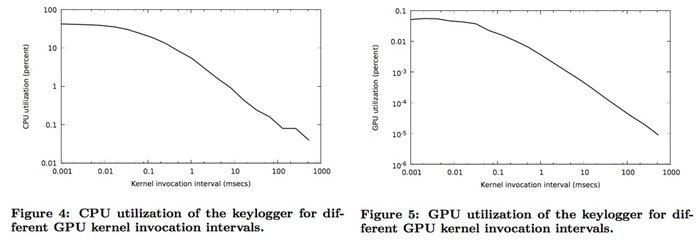
Figures 4 and 5 show the keylogger’s CPU and GPU utilization when varying the GPU kernel invocation interval. Typically, the duration of a single keypress varies from 100 ms for faster typists, to over one second for slower typists [14]. Consequently, the GPU invocation interval should be kept under 100 ms, to enable accurate monitoring of all key presses, without missed events. As shown in both figures, we have chosen an interval of 90 ms, which has minimal performance impact: the CPU utilization is about 0.1% (Figure 4), while the GPU has negligible utilization of 5×10^−5 % (Figure 5). The time needed by the GPU to read the contents of the 8-byte keyboard buffer over the PCIe bus is about 0.005 ms.
[You Can Type, but You Can’t Hide: A Stealthy GPU-based Keylogger]
実際VISAやMasterCardなどのクレジットカードナンバーを異なるサイズのバッファからクレジットカードナンバーの正規表現を使用して抽出するまでの時間測定しています。
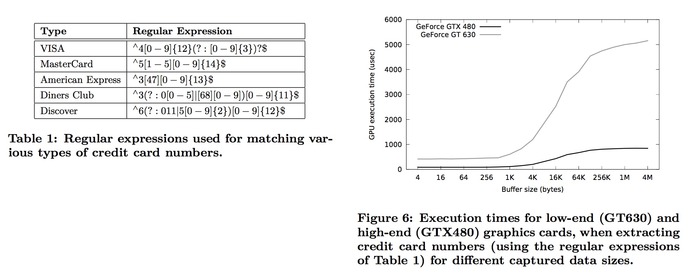
In the next experiment, we measure the time needed by the GPU to scan the captured data and extract sensitive information. Specifically, we search the recorded data for various types of credit card numbers, using the regular expressions shown in Table 1. Figure 6 shows the corresponding GPU execution times for different input sizes. We observe that the running times are below one millisecond even for buffer sizes in the order of Megabytes. As such, the scanning over- head is negligible, given that the average user needs several seconds to type a few hundred of bytes.
[You Can Type, but You Can’t Hide: A Stealthy GPU-based Keylogger]
MAC_JELLY
Jellyfish Teamは既にCUDA SDKとドライバー、NVIDIA GPU、Windows APIを使用して動作するWindows版 Jellyfishのリモート アクセス ツール(RAT)「WIN_JELLY」を公開しており、現在Mac版Jellyfish「MAC_JELLY」の開発も進めているそうで、

一昨日更新されたリポジトリには「Mac OS X版Jellyfishの開発を行っており、OS XにはOpenCLがプリインストールしてあり非常に面白い」とコメントしている一方、GPUベースのマルウェアを特定するためのツール「JellyScan」も開発している様です。
Judging by Team Jellyfish’s GitHub repository, the developers also plan to create a version for Mac OS X called MAC_JELLY. They also noted in the description of their Linux rootkit that “Mac OS X boxes come pre-installed with OpenCL.”
On the defense side, the team is also working on a tool called JellyScan that will allow system administrators and security researchers to detect GPU-based malware.
[Stealthy Linux GPU malware can also hide in Windows PCs, maybe Macs – PCWorld]
関連リンク:
・x0r1 – GitHub
・GPU-based rootkit and keylogger offer superior stealth– Ars Technica
・GPU malware can also hide in Windows PCs, maybe Macs – PCWorld



コメント
話しがマニアック過ぎてついていけない…。
米1
GPGPUはまだ一部の人しか恩恵ないけどこれから発展していく分野だから、数年するとこういうのが当たり前になると思うよ。
独自GPUを使ってるMacはどうなるか知らんけど
Macは別に独自GPUなんて使ってないよ
汎用品だし、接続はOpenCLだし
ヘタしたら、windowsよりもMacのの方が、これの親和性が高いんじゃねぇの?
GPGPUはWi-Fiの暗号化(WPA2、AESキー)も解読できるからな
こういう方向に進むのは見てて面白いわ
GPU活用系は、blenderやoculusの様にMacが不利だと思う。
GPUのアップグレードが不可能だから。
んびでぃあ と あむど
にしてもマルウェアは勘弁。
マルウェアの実装と検出方法を同時に開発とかひとりいたちごっこというかマッチポンプというか、
最終的には類似技術がみなでてくるのは分かっていてもなんか釈然としない。